DoD Announces major changes with CMMC 2.0
The DoD has announced a major overhaul to CMMC with version 2.0 of the program. The new model is still based on NIST 800-171, with the major changes being around how assessments are performed, the allowance of Plan of Actions and Milestones (POA&Ms), and allowance for limited waivers for specific CMMC requirements. What is clear […]
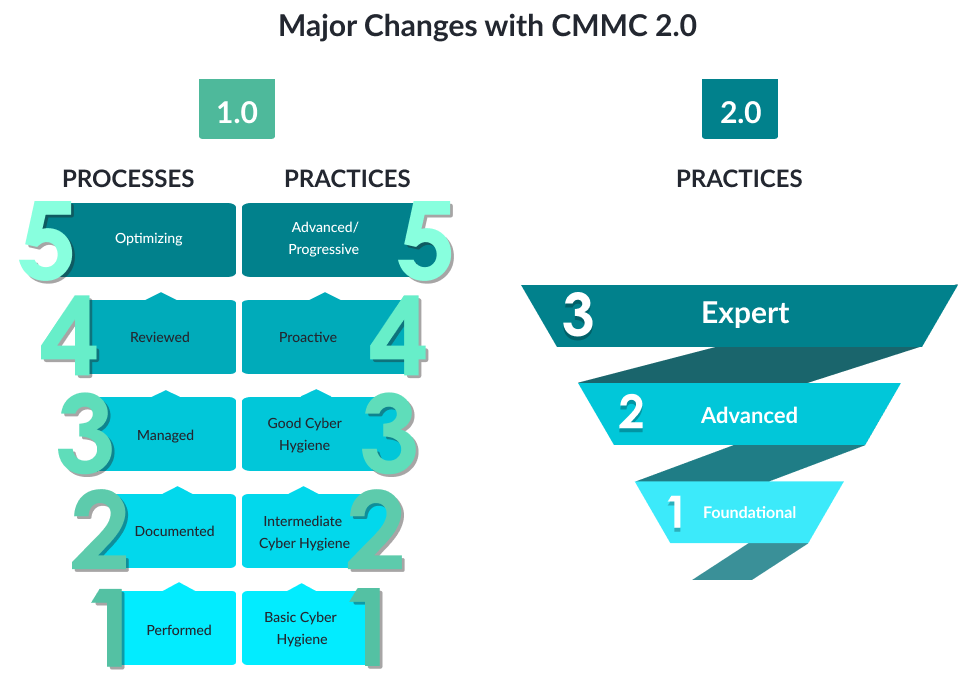
The DoD has announced a major overhaul to CMMC with version 2.0 of the program. The new model is still based on NIST 800-171, with the major changes being around how assessments are performed, the allowance of Plan of Actions and Milestones (POA&Ms), and allowance for limited waivers for specific CMMC requirements.
What is clear is that there will be 3 progressive levels; Foundational, Advanced, and Expert.
The major changes to attestations are based on the level and the type of data in the environment.
New CMMC Level 1
Level 1 (Foundational) will consist of 17 practices that cover basic cybersecurity hygiene. This will more than likely mirror the existing 17 practices that are a requirement for protecting Federal Contract Information (FCI). This level will require annual self-attestation much like current the current SPRS process.
New CMMC Level 2
Level 2 (Advanced) consists of the 110 controls from NIST 800-171 and has two separate attestation requirements depending the type of data in the organization. For a specific subset of Level 2, annual self-attestations will be required. For Level 2 organizations that “involve information critical to national security”, which sounds an awful lot like Controlled Unclassified Information (CUI). Those organizations will require an independent audit from a C3PAO by a Certified Assessor.
New CMMC Level 3
Level 3 (Expert) consists of the 110 controls controls from NIST 800-171 along with the enhancements from NIST 800-172 and focuses on protecting against Advanced Persistent Threats (APTs). This level will require a government led assessment, which will most likely be similar to the current DIBCAC assessments.
The required level will be specified in the solicitation and/or Request for Information (RFI). Realistically you can expect to see upstream customers (primes) push requirements to their subcontractors regardless of actual DFARS requirements. We’ve seen that a lot in the past with contractual clauses containing requirements to “demonstrate level 3 readiness”.
CMMC v2.0 also introduces the acceptance of a Plan of Actions and Milestones (POA&Ms). A POA&M is a document that describes your roadmap for addressing any identified non-conformities or issues that require remediation (for instance, unacceptable organizational risks). Your POA&M allows you to track, timeline, and resource improvements to your cybersecurity program.
So what can you do now?
The DFARS requirements have not gone away and are still the regulations which govern the DIB. Continue working on improving cybersecurity practices and maintaining your SPRS score, the requirements to protect FCI and CUI have not gone away or changed.
- Track the implementation and effectiveness of your cybersecurity program against CMMC v2.0 requirements
- Maintain your SSP
- Create a POA&M and begin tracking cybersecurity activities
CMMCplus is a modern easy to use tool created to help build, track, test, and demonstrate CMMC compliance. Get started with a free gap assessment today at CMMCplus.com











